Beyond OWASP 2026: Advanced Web Exploitation Techniques & Secure Coding Defense Playbook
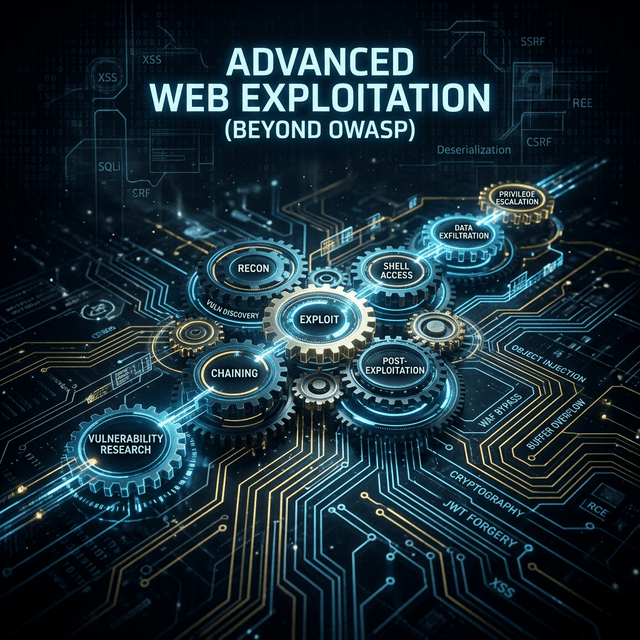
Beyond OWASP 2026: Advanced Web Exploitation Techniques & Secure Coding Defense Playbook
While the OWASP Top 10 remains a baseline, 2026 web security requires defending against complex exploit chains, serverless logic flaws, and decentralized API attacks. This playbook dives into the advanced techniques used by modern adversaries.
1. Logic Flaws
Automated scanners often miss complex business logic flaws. We explore how multi-stage authentication bypasses and race conditions in financial transaction modules can lead to full system compromise without triggering a single alert. These are the "silent killers" of modern web apps.
2. Chained Exploits
A 'Low' severity XSS combined with a 'Medium' severity SSRF can lead to 'Critical' internal network access. We demonstrate how to chain multiple minor vulnerabilities to achieve Remote Code Execution (RCE). Chaining is the key to bypassing modern cloud firewalls.
3. API & Microservices
With the explosion of GraphQL and gRPC, traditional REST security is not enough. We analyze advanced introspection attacks, broken object-level authorization (BOLA), and mass assignment vulnerabilities in modern microservice architectures.
4. Client-Side Exploitation
The browser is now a powerful execution environment. We dive into DOM-based vulnerabilities, client-side prototype pollution, and cross-site leaks (XS-Leaks) that compromise user data without ever hitting the server.
5. Secure Coding Countermeasures
Defense is just as important as offense. We provide a 'Secure Coding Playbook' for React and Next.js developers, focusing on input sanitization, secure headers, and zero-trust authentication patterns.
Conclusion
Staying ahead of web threats requires a mindset shift from 'scanning' to 'modeling'. By understanding advanced exploitation techniques, developers can build inherently secure systems that resist the attack chains of tomorrow.
CTA
Secure your development lifecycle. Connect with me to implement advanced AppSec testing and secure coding workshops for your engineering team.
Frequently Asked Intel
Why is exploit chaining so effective?
It bypasses individual security controls that only look for specific patterns. By combining minor flaws, attackers can create a 'critical' impact that triggers fewer alarms.
Can these techniques be automated?
To an extent, but the most dangerous logic flaws and chains require a human attacker's intuition to identify and execute.
How do I start implementing secure coding?
Start with a strict Content Security Policy (CSP) and ensure all developers are trained in identifying common pitfalls like prototype pollution and BOLA.
Related_Discovery
Expand Your Knowledge
How I Use Nmap for Advanced Network Reconnaissance
An exhaustive guide to advanced Nmap techniques. Learn the clandestine methodologies used by top VAPT Specialists in India to map attack surfaces and bypass modern IDS/IPS systems.
OWASP Top 10 Explained with Real Exploitation Examples
A comprehensive deep-dive into the OWASP Top 10. Learn about the most critical web security vulnerabilities with real-world exploit scenarios from an Advanced Web Penetration Testing expert.
Automating Web Security Testing with Burp Suite
Learn how to transform Burp Suite into an automated security powerhouse. A guide for professional Penetration Testers on scaling vulnerability discovery with Security Automation.