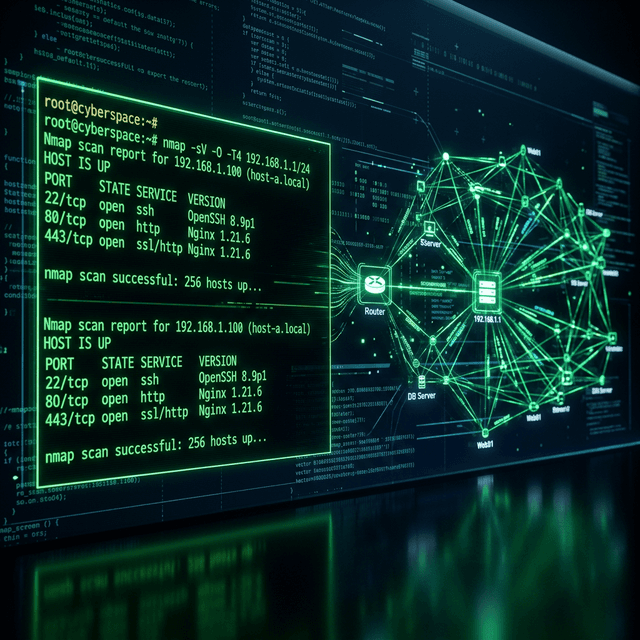
How I Use Nmap for Advanced Network Reconnaissance
An exhaustive guide to advanced Nmap techniques. Learn the clandestine methodologies used by top VAPT Specialists in India to map attack surfaces and bypass modern IDS/IPS systems.
Comprehensive methodologies on VAPT, advanced exploitation, and defensive hardening. Documenting the frontier of offensive security.
An exhaustive guide to advanced Nmap techniques. Learn the clandestine methodologies used by top VAPT Specialists in India to map attack surfaces and bypass modern IDS/IPS systems.

A comprehensive deep-dive into the OWASP Top 10. Learn about the most critical web security vulnerabilities with real-world exploit scenarios from an Advanced Web Penetration Testing expert.
Learn how to transform Burp Suite into an automated security powerhouse. A guide for professional Penetration Testers on scaling vulnerability discovery with Security Automation.
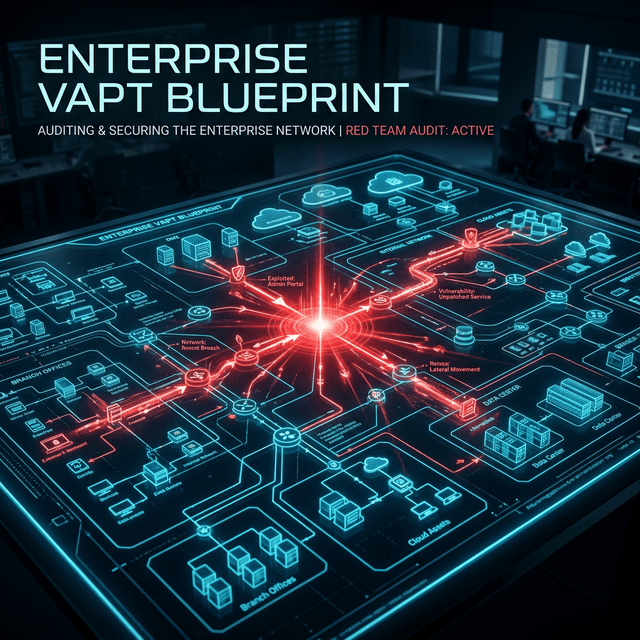
Explore a complete VAPT methodology for modern enterprises in 2026. Step-by-step penetration testing, red team engagements, and network security auditing techniques for ethical hackers.
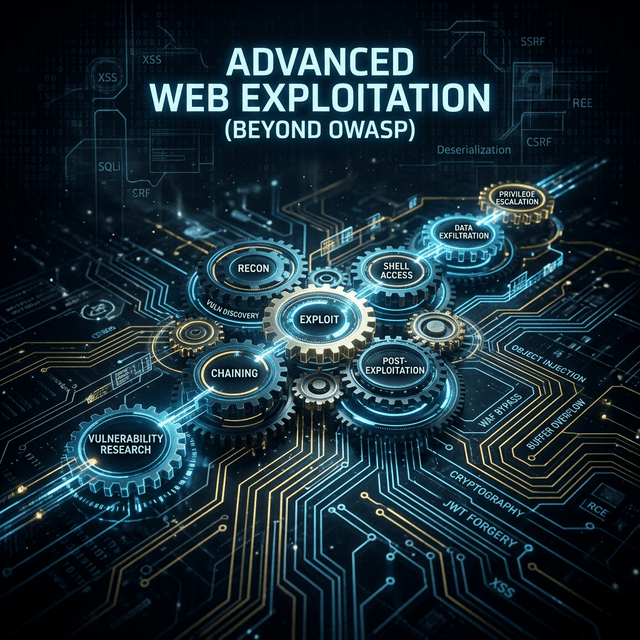
Master advanced web exploitation techniques and secure coding defensive measures. Learn real-world attack chains, API vulnerabilities, and how to defend modern web applications.