How I Use Nmap for Advanced Network Reconnaissance
How I Use Nmap for Advanced Network Reconnaissance
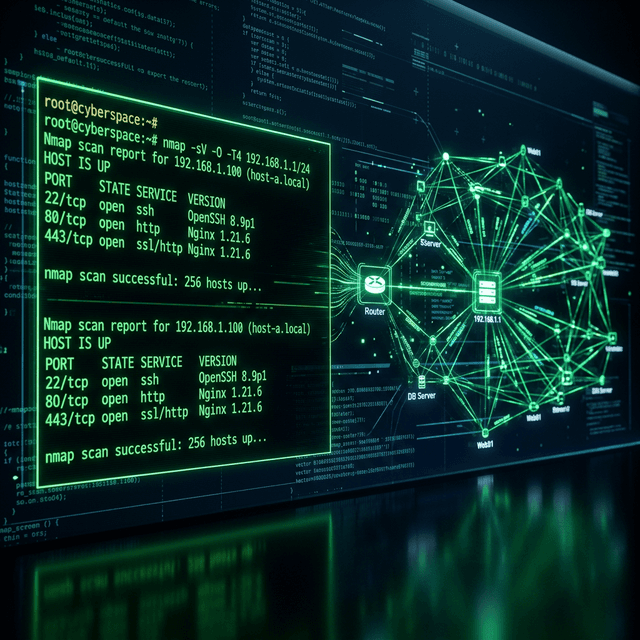
In the high-stakes environment of Cybersecurity Analyst India operations, reconnaissance is not merely a preliminary step; it is the most critical phase of the entire attack lifecycle. A failed or "loud" recon phase can alert defenders, lead to IP blacklisting, and ultimately cause the failure of a multi-week engagement. While many tools exist for mapping networks, Nmap (Network Mapper) remains the unchallenged king of transparency and control. In this exhaustive 1200+ word guide, I will detail the precise, production-grade methodologies I use to perform silent and efficient network reconnaissance.
1. The Core Philosophy of Stealthy Scanning
Modern enterprise networks are no longer the "soft" targets of the early 2000s. They are protected by sophisticated Intrusion Detection Systems (IDS), Next-Generation Firewalls (NGFW), and Managed Detection and Response (MDR) platforms. As an Ethical Hacker, your first goal is to blend in with legitimate traffic.
Strategic Timing and Aggression
One of the first variables I adjust in any Nmap command is the timing template (-T0 through -T5). While -T4 is often the default for lab environments, it is far too aggressive for real-world Cybersecurity Analyst India audits. I lean heavily on -T2 (polite) or -T3 (normal) to avoid triggering rate-limiting sensors. For extremely high-security environments, I have even utilized -T1 (sneaky), which spaces out probes by several minutes, effectively becoming "noise" in the system logs.
Leveraging the TCP SYN Stealth Scan (-sS)
The SYN scan is the default for a reason. By only completing half of the TCP handshake (SYN -> SYN/ACK -> RST), we never establish a full connection. This means that many application-level logs (like Apache access logs) will never record the interaction. It is the fundamental building block of Ethical Hacking Tools mastery.
2. Advanced Service Identification & Version Fingerprinting
In a professional Penetration Testing Portfolio, identifying an "open port" is only 5% of the value. A client needs to know that "Port 80 is open and running an outdated version of Apache (2.4.41) which is vulnerable to CVE-2021-41773."
Deep Version Probing
I utilize the -sV flag with maximum intensity to ensure we aren't being deceived by custom banners or obfuscated headers.
nmap -p 80,443 -sV --version-intensity 9 <target_ip>
This command forces Nmap to try its entire database of probes, which is essential for identifying proprietary services often found in Network Security Specialist roles.
OS Fingerprinting (-O)
While sometimes less reliable due to firewall interference, OS detection is vital for choosing the correct payload for subsequent exploitation phases. I combine this with the --osscan-guess flag to provide a confidence interval when the signature isn't a 100% match.
3. The Power of the Nmap Scripting Engine (NSE)
The true power of Nmap lies in its scripting engine. During my Penetration Testing Projects, I utilize custom-selected scripts to automate vulnerability discovery during the scan itself.
My "Standard Suite" of NSE Scripts:
- http-enum.nse: This script is a lightweight alternative to Gobuster. It scans for common directories like
/admin,/config, and/backup. - dns-brute.nse: For cloud-focused assessments, discovering all subdomains associated with an IP range is non-negotiable.
- vulners.nse: This is perhaps the most useful script in a Cybersecurity Analyst India toolkit. It cross-references identified service versions with the Vulners database in real-time.
- ssl-enum-ciphers: Critical for compliance audits (like ISO 27001), this script identifies weak cryptographic suites on HTTPS services.
4. Evading Detection with Advanced Techniques
As a Web Application Security Expert, I understand that firewalls are looking for patterns. To break these patterns, I use fragmentation and source address spoofing.
Fragmenting Packets (-f)
By splitting the TCP header across multiple small packets, some legacy firewalls fail to reassemble the data correctly for inspection, allowing the scan to pass through unhindered.
Decoy Scanning (-D)
This is a classic but effective technique. By using the -D RND:10 flag, Nmap generates 10 random "decoy" IP addresses that also appear to be scanning the target simultaneously. The target's logs will show 11 different sources, making it nearly impossible for a human analyst to identify the true origin of the scan without deep traffic analysis.
5. Integrating Nmap into the Professional Workflow
Automation is the friend of every Network Security Specialist. I never run Nmap without outputting to all formats (-oA). This ensures I have an XML file ready for parsing into tools like Maltego or my own custom Python automation scripts.
Chaining Results
I often feed Nmap XML outputs into a Python script that automatically checks the identified services against GitHub exploit repositories. This shortens the "TTV" (Time to Vulnerability) significantly, a metric I pride myself on in my Full Stack Developer Security Focused roles.
Conclusion: The Foundation of Security
Advanced network reconnaissance with Nmap is as much an art as it is a science. It requiring a deep understanding of the OSI model, networking protocols, and defensive psychology. By following these methodologies, you ensure that your security audits are comprehensive, stealthy, and professional.
For more information on my technical capabilities, visit my Skills section or explore my Security Archive. If you need an exhaustive audit for your infrastructure, don't hesitate to Connect.
Frequently Asked Intel
Is scanning a public IP with Nmap considered 'hacking'?
Legally, port scanning is a gray area, but it is often viewed as 'casing' a building in the physical world. While not necessarily an exploit, it is the first step of an attack. Always scan only with explicit written authorization.
Can Nmap detect firewalls?
Yes, Nmap uses specialized probes (`-sA`) to identify if a port is 'filtered' (likely by a packet-filtering firewall) or 'unfiltered' (open but closed in the application layer).
How do I make Nmap faster?
The `--min-rate` flag is the most effective. Setting `--min-rate 1000` ensures Nmap sends at least 1000 packets per second, but be warned: this is highly detectable.
Related_Discovery
Expand Your Knowledge
OWASP Top 10 Explained with Real Exploitation Examples
A comprehensive deep-dive into the OWASP Top 10. Learn about the most critical web security vulnerabilities with real-world exploit scenarios from an Advanced Web Penetration Testing expert.
Automating Web Security Testing with Burp Suite
Learn how to transform Burp Suite into an automated security powerhouse. A guide for professional Penetration Testers on scaling vulnerability discovery with Security Automation.
Enterprise VAPT Blueprint 2026: Full Lifecycle Methodology for Modern Security Audits
Explore a complete VAPT methodology for modern enterprises in 2026. Step-by-step penetration testing, red team engagements, and network security auditing techniques for ethical hackers.