Enterprise VAPT Blueprint 2026: Full Lifecycle Methodology for Modern Security Audits
Enterprise VAPT Blueprint 2026: Full Lifecycle Methodology for Modern Security Audits
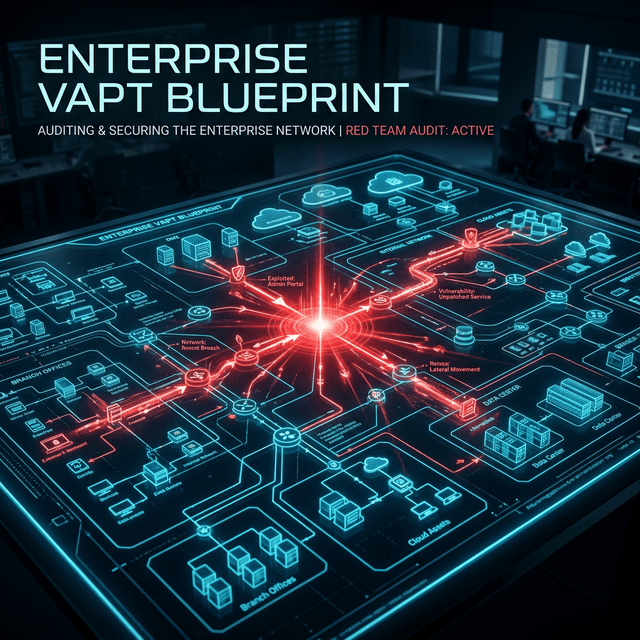
In 2026, the digital attack surface has evolved from simple web endpoints to complex multi-cloud environments, decentralized identifiers (DIDs), and AI-driven microservices. A traditional Vulnerability Assessment and Penetration Testing (VAPT) approach is no longer sufficient. This blueprint outlines a holistic methodology designed for high-stakes enterprise environments.
1. Planning & Scoping
Effective audits begin with clear boundaries. We define the search space (ASN, CIDR, Cloud Assets), identify critical business processes, and establish the Rules of Engagement (ROE). This ensures zero impact on production while maximizing high-value vulnerability discovery.
2. Reconnaissance
Before a single packet is sent, we leverage modern reconnaissance techniques. From passive DNS monitoring to discovering forgotten shadow IT assets, we map the external posture of the organization through an attacker's lens. This phase is critical for Cybersecurity Analyst India operations.
3. Threat Modeling
Not all vulnerabilities are created equal. We model threats based on current adversary techniques (MITRE ATT&CK framework). We ask: "How would a state-sponsored actor or a sophisticated ransomware group target this specific infrastructure?"
4. Exploitation
This phase moves from theory to practice. We attempt to bypass security controls using custom exploits, credential stuffing, and logic flaw manipulation. The goal isn't just to 'break in' but to demonstrate the actual business risk of an unpatched vulnerability.
5. Post-Exploitation & Reporting
The real value of VAPT lies here. We analyze lateral movement possibilities and data exfiltration vectors. Our final reports provide clear, actionable remediation steps for developers and executive summaries for stakeholders.
6. Continuous Improvement
Security is not a destination. We provide post-audit support to verify fixes and perform delta-testing. We also recommend periodic red-teaming to challenge the blue team's detection capabilities. This continuous loop of feedback and hardening is the hallmark of an elastic security posture.
Conclusion
A 2026-ready VAPT lifecycle is a continuous loop of testing, patching, and hardening. By adopting this rigorous blueprint, enterprises can stay ahead of the curve and maintain a truly resilient security posture.
CTA
Ready to secure your enterprise? Get in touch for a comprehensive VAPT audit tailored to your infrastructure.
Frequently Asked Intel
How often should an enterprise undergo VAPT?
At minimum, once per year or after any significant infrastructure change. However, for high-risk targets, continuous security monitoring or quarterly audits are recommended.
What is the difference between VA and PT?
Vulnerability Assessment (VA) is the process of identifying vulnerabilities, while Penetration Testing (PT) involves actively exploiting them to verify their impact.
Is this methodology compliant with SOC2 or ISO 27001?
Yes, this lifecycle exceeds the requirements for standard compliance frameworks, focusing on real-world risk rather than just checking boxes.
Related_Discovery
Expand Your Knowledge
How I Use Nmap for Advanced Network Reconnaissance
An exhaustive guide to advanced Nmap techniques. Learn the clandestine methodologies used by top VAPT Specialists in India to map attack surfaces and bypass modern IDS/IPS systems.
OWASP Top 10 Explained with Real Exploitation Examples
A comprehensive deep-dive into the OWASP Top 10. Learn about the most critical web security vulnerabilities with real-world exploit scenarios from an Advanced Web Penetration Testing expert.
Automating Web Security Testing with Burp Suite
Learn how to transform Burp Suite into an automated security powerhouse. A guide for professional Penetration Testers on scaling vulnerability discovery with Security Automation.